About this website
To set up information security within your organization, a number of standards can be used, like ISO/IEC 27002. These standards contain many controls that help to get a grip on information security. However, implementing a control without having insight into the 'how & why' behind the control, is not efficient. Therefore, it is advisable to first determine what the risks are and then to determine which controls are useful to address those risks.
This website offers you a tool to perform a risk analysis for information security. The outcome of this tool is a list of ISO/IEC 27002 controls, which can be used to reduce the risks for your organization to an acceptable level.
RAFIS is based on an approach consisting of the following steps and provides support for the first four steps.
- The first step is to perform a business impact analysis, in which the important information systems of your organization are mapped. The goal of this step is to determine the importance of each information system for the organization and the requirements with regard to the confidentiality, integrity and availability of the information stored therein.
- The second step is to identify actors that could potentially breach information security.
 The next step is to determine the threats that are plausible to the organization. For each threat, it is determined to what extent the threat is real for your organization and which mitigating approach is desirable. RAFIS contains a list of generic threats that you can use to identify a threat specific to your organization. The level of each threat is determined via a risk matrix.
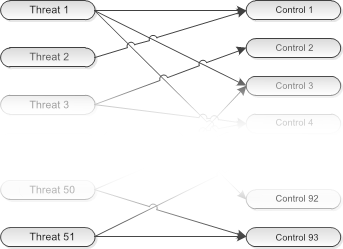
The next step is to determine the threats that are plausible to the organization. For each threat, it is determined to what extent the threat is real for your organization and which mitigating approach is desirable. RAFIS contains a list of generic threats that you can use to identify a threat specific to your organization. The level of each threat is determined via a risk matrix.- Then, from the list of threats and the desired approach, the corresponding controls from the ISO/IEC 27002 standard can be selected. If you have used the threat list available in RAFIS, RAFIS will suggest possible controls for each identified threat via a link to the ISO/IEC 27002 controls.
- Finally, the list of controls must be converted into a concrete action plan for organizing information security within your organization. For this, you must be in possession of the ISO/IEC 27002 standard. In it, the individual controls are described in concrete steps to be taken.
After going through these steps, you will be better prepared for a possible ISO/IEC 27001 certification. An extensive description of how to perform risk analysis with RAFIS can be found in the documentation.
This tool was developed by Hugo Leisink. He has many years of experience as an information security consultant and information security officer. You can read information about the security, availability and privacy of this tool in this statement. Questions or comments can be sent via the contact form.